A Cloud KMS signer uses a signing key generated and stored inside a cloud key management service — AWS KMS, Azure Key Vault, or GCP Cloud HSM. The key is non-extractable by design: no employee at your company (or at the cloud provider) can ever retrieve the raw key material. Cloud KMS signers support advanced enterprise security controls natively, including IP allowlisting, cloud IAM-based access policies, rate limiting, circuit breakers, and detailed audit logs and alerting. For a conceptual overview, see Cloud KMS in the Wallet Signers guide. To learn how to register additional operational signers on an existing wallet, see Registering a signer.Documentation Index
Fetch the complete documentation index at: https://docs.crossmint.com/llms.txt
Use this file to discover all available pages before exploring further.
- Google Cloud KMS
- AWS KMS
How It Works
- You create a signing key inside Google Cloud KMS — the private key never leaves Google’s hardware.
- A Cloud Run function sits in front of KMS and signs transaction digests on demand.
- The Crossmint SDK calls your Cloud Run function whenever the wallet needs to sign something.
- The signature is converted from Google’s format to Ethereum’s format, and the Crossmint SDK uses it to complete the transaction.
What You Will Build
- An asymmetric signing key in Google Cloud KMS (secp256k1)
- A Cloud Run function that signs digests via KMS
- A Crossmint server wallet using your KMS key as its signer
Prerequisites
- A Google Cloud project with billing enabled
- A Crossmint server API key
- Node.js 18+
Set Up Google Cloud KMS
Enable the Cloud KMS API
Navigate to Cloud Key Management in the Google Cloud Marketplace and click Enable.
Create a Key Ring
Go to Security > Key Management in the Google Cloud Console and click Create Key Ring.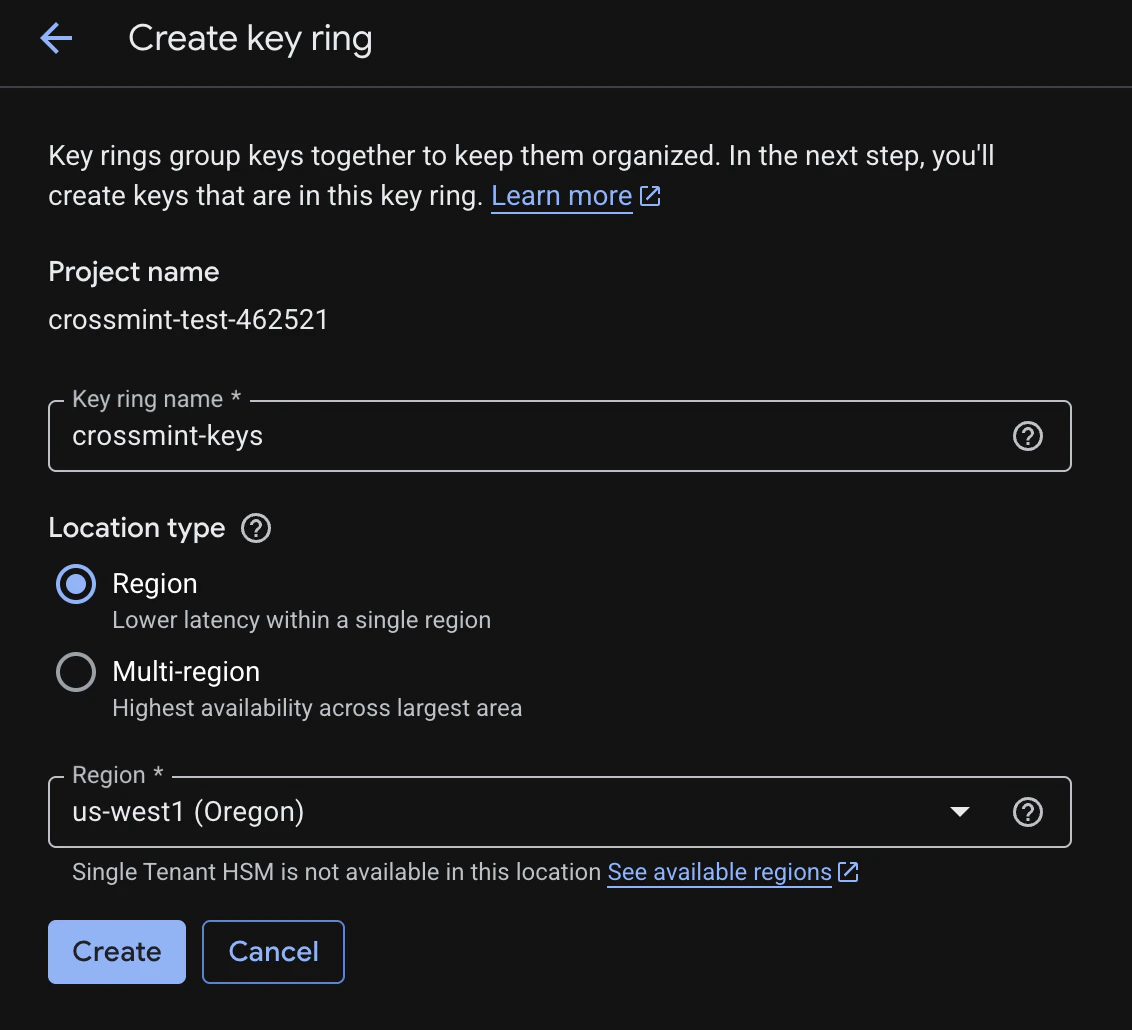
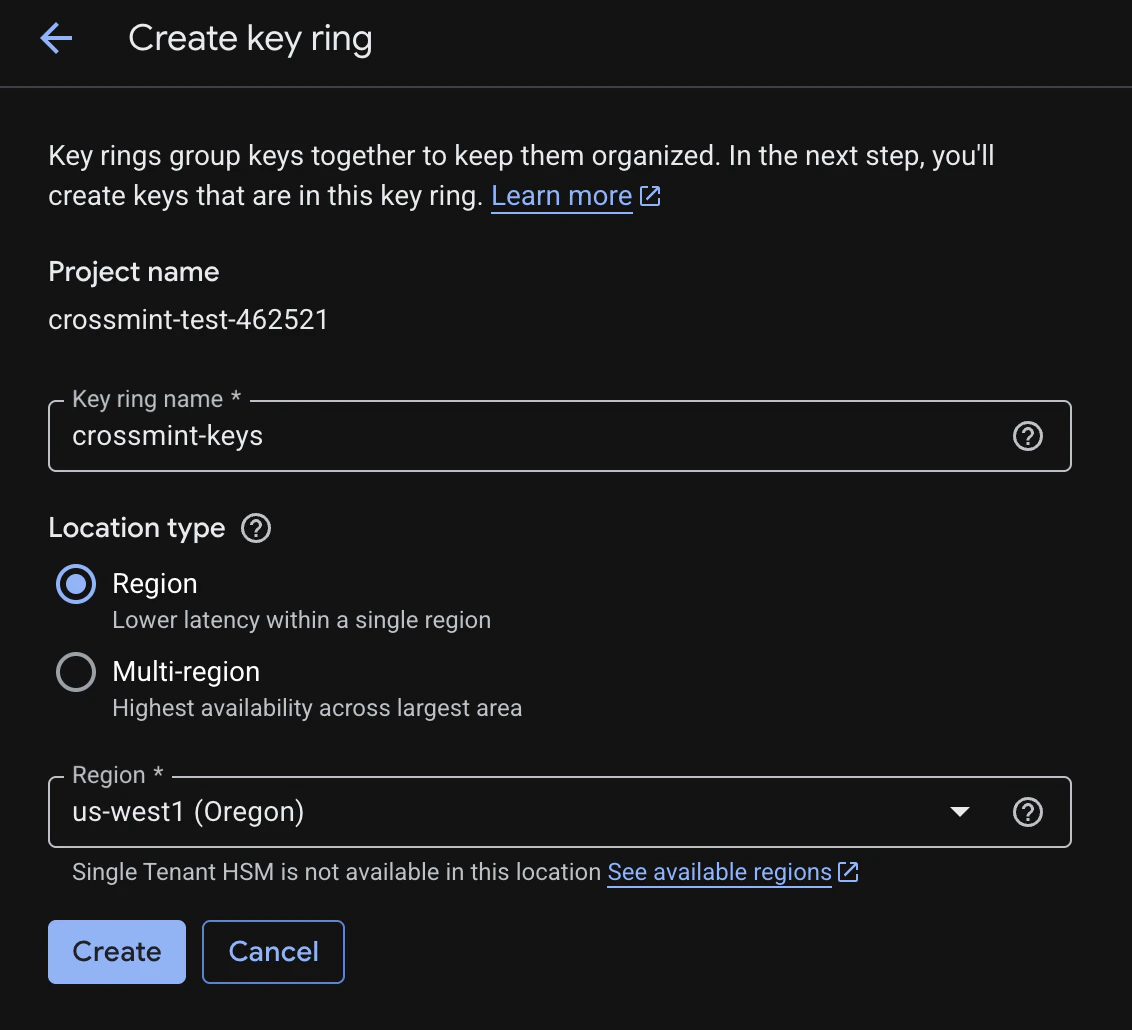
- Key ring name:
crossmint-keys(or your preferred name) - Location: Select a region, e.g.
us-west1
Create an Asymmetric Signing Key
Inside your key ring, click Create Key with the following settings: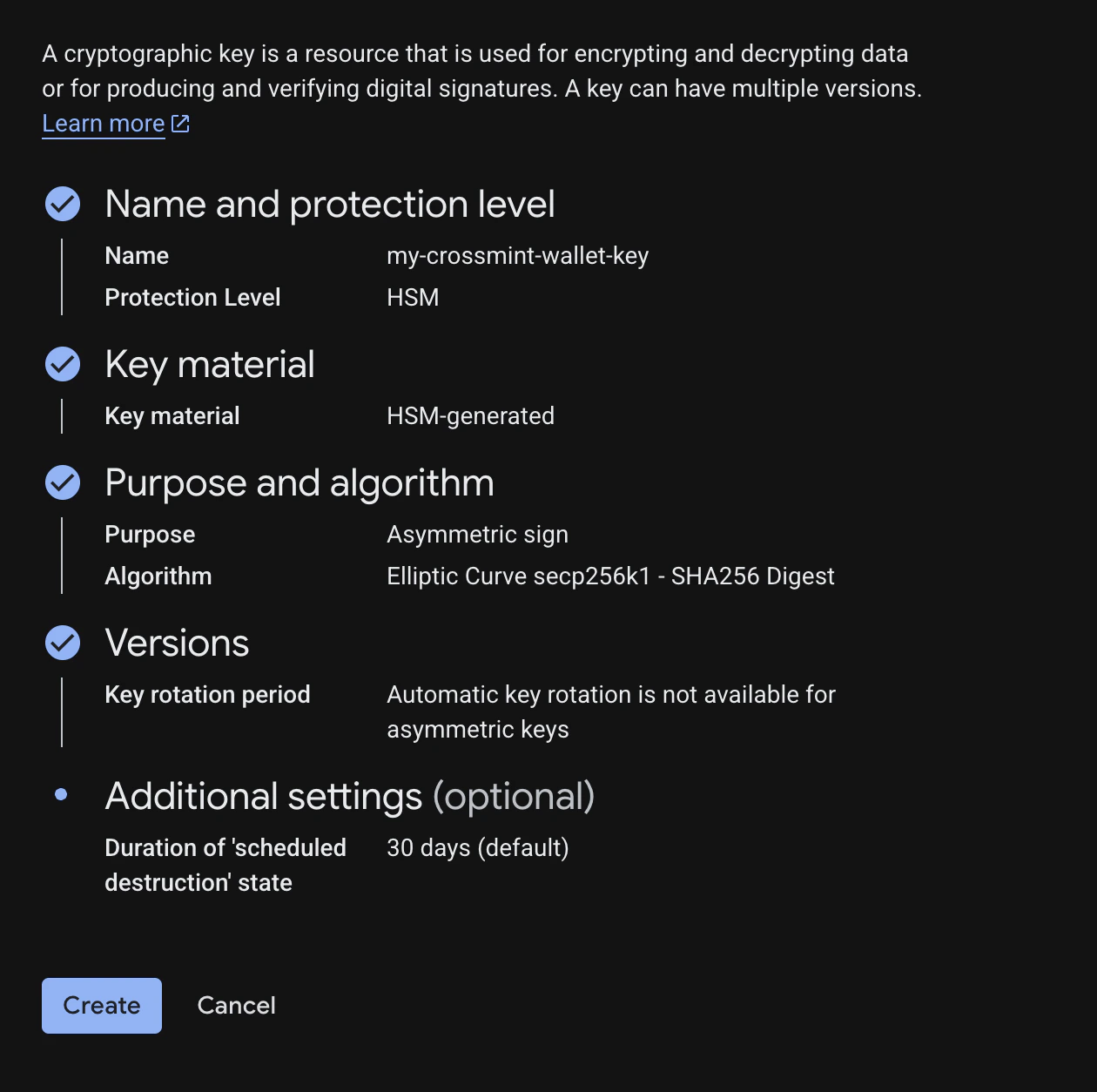
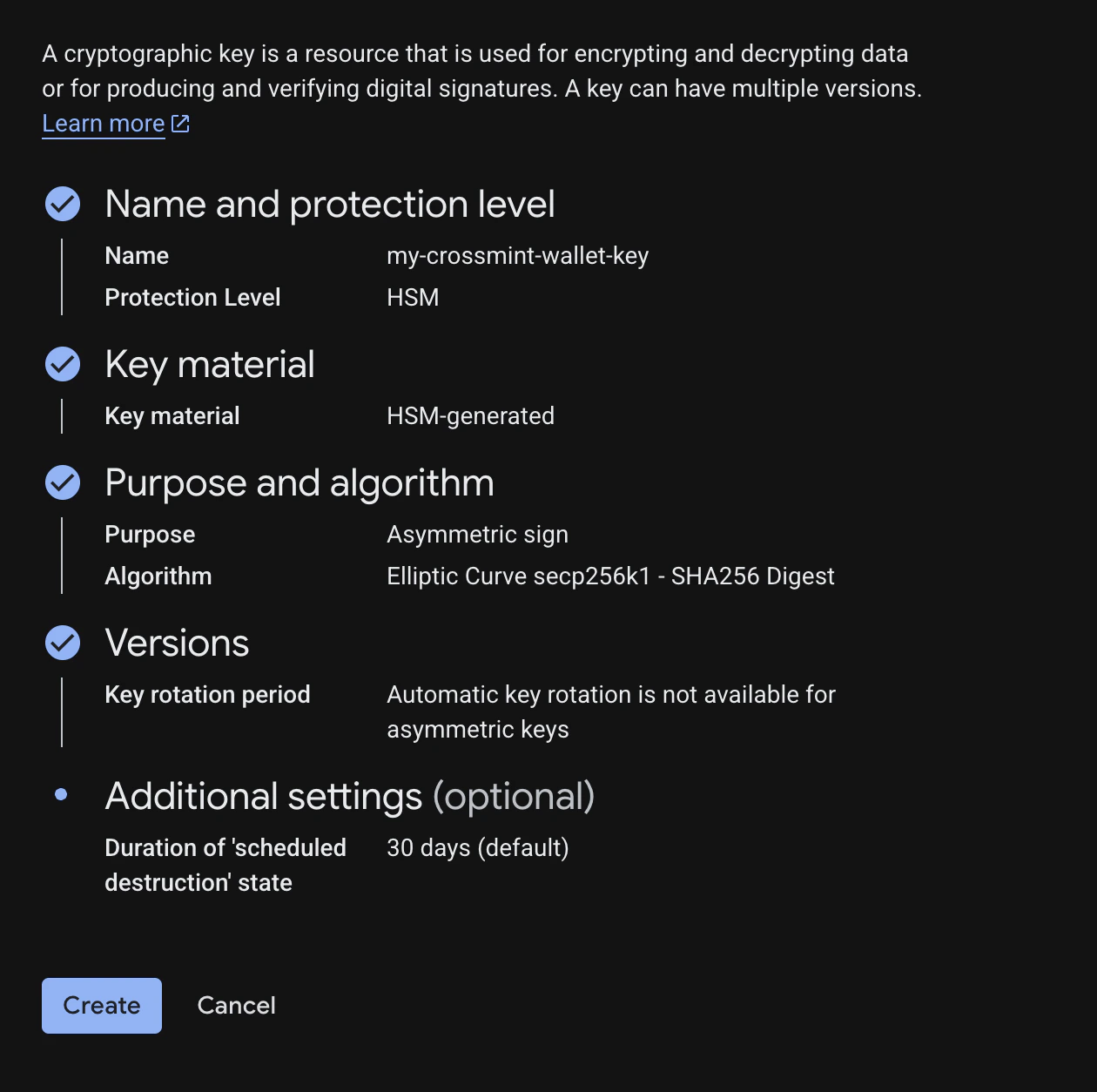
| Setting | Value |
|---|---|
| Key name | my-crossmint-wallet-key |
| Protection level | HSM (Hardware Security Module) |
| Key material | HSM-generated key |
| Purpose | Asymmetric Sign |
| Algorithm | Elliptic Curve secp256k1 - SHA256 Digest |
Set Up IAM Permissions
Create a Service Account
Navigate to IAM & Admin > Service Accounts and create a new service account (e.g.
kms-signer-sa).Deploy a Cloud Run Signing Function
This function receives a digest, signs it with your KMS key, and returns the DER-encoded signature.Create a Cloud Run Function
Go to Cloud Run Functions and create a new function:
- Name:
kms-signer-function - Region: Same region as your key ring (e.g.
us-west1) - Runtime: Node.js 18+
- Authentication: Configure based on your security requirements
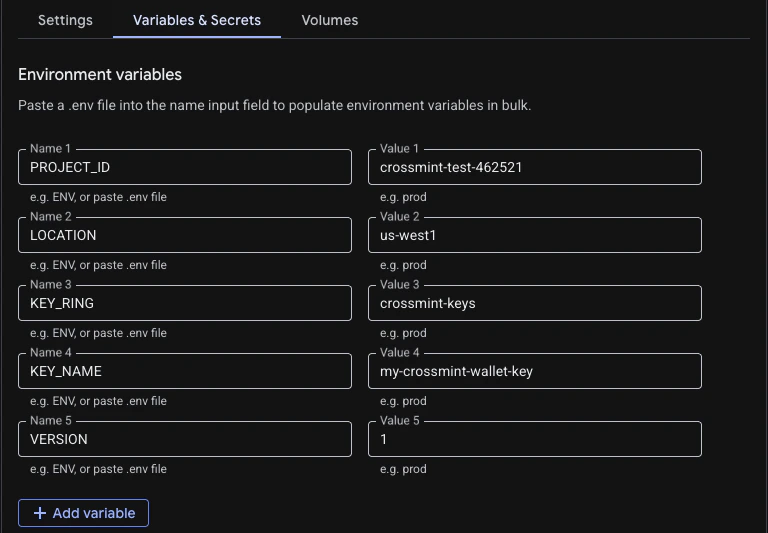
Set Environment Variables
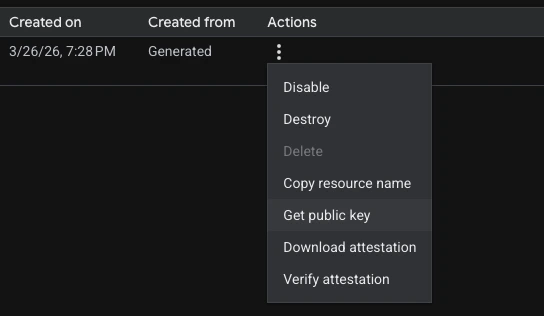
In the Cloud Run function settings, go to the Containers tab, expand Edit Container, then select the Variables & Secrets tab. Add the following environment variables. To get these values, use Copy resource name from the same key version actions menu where you downloaded the public key — it gives you a path like
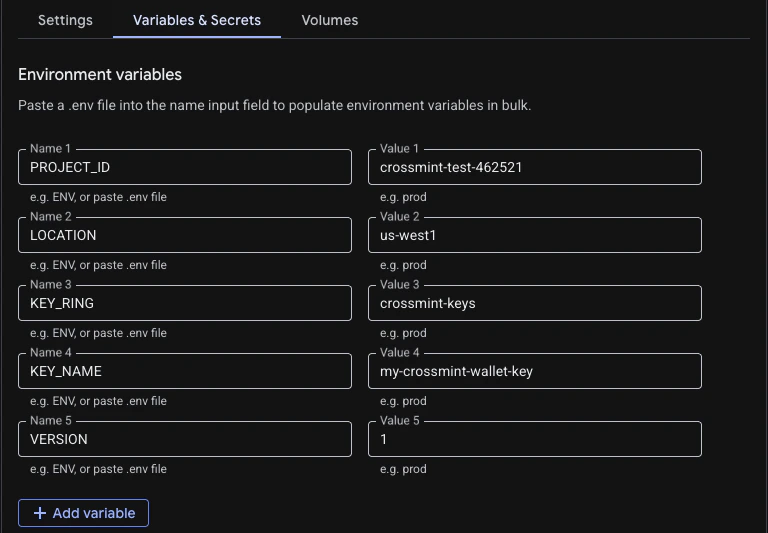
projects/PROJECT_ID/locations/LOCATION/keyRings/KEY_RING/cryptoKeys/KEY_NAME/cryptoKeyVersions/VERSION.| Variable | Example Value |
|---|---|
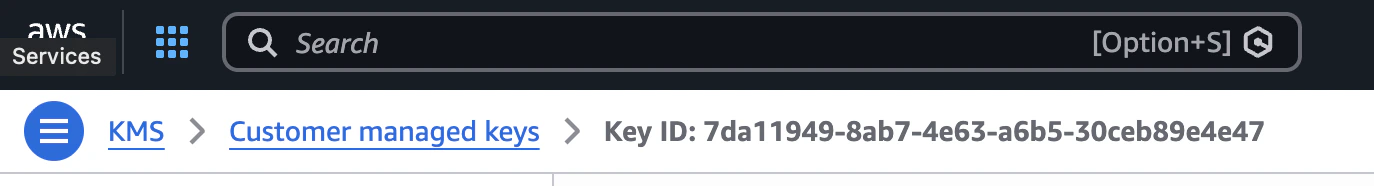
PROJECT_ID | crossmint-test-462521 |
LOCATION | us-west1 |
KEY_RING | crossmint-keys |
KEY_NAME | my-crossmint-wallet-key |
VERSION | 1 |
Add the Function Code
Set the Function entry point to Add 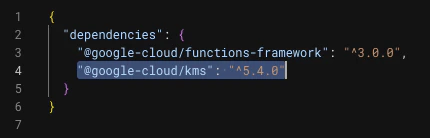
signDigest, then paste the following code:index.js
@google-cloud/kms to your function’s package.json dependencies:
Create and Use the Crossmint Wallet
Now wire everything together — convert your KMS public key to an Ethereum address, create a Crossmint wallet, and sign transactions through your Cloud Run function.Install Dependencies
Convert the KMS Public Key to an Ethereum Address
Google Cloud KMS returns public keys in PEM/DER format. This helper extracts the raw public key bytes and converts them to an Ethereum address usingviem.kms-utils.ts
Build the KMS Signing Function
Cloud KMS returns DER-encoded signatures. Ethereum requiresr, s, v format with EIP-2 low-s normalization. This function handles the full conversion:kms-signer.ts
Create the Wallet
Use the KMS-derived Ethereum address as the wallet’s recovery signer. The recovery signer is used for wallet recovery and adding new signers — ideal for a server-held KMS key.create-wallet.ts
Use the Wallet
Once created, retrieve the wallet and use it to sign transactions. Here are a couple of examples:use-wallet.ts
Security Best Practices
Key rotation caveat: While Cloud KMS supports automatic key rotation,
rotating an asymmetric signing key generates a new key pair — which means a
new Ethereum address. For wallets, manage key versions carefully and plan
migrations accordingly.
- Restrict Cloud Run access: Use IAM authentication or VPC Service Controls to ensure only authorized services can call your signing function.
- Enable audit logs: Turn on Cloud KMS “Data Access” audit logs to track every signing operation.
- Principle of least privilege: Only grant the
signerVerifierrole — never grantadminorencrypterDecrypterroles to your signing service account. - Environment variables: Never hardcode your Crossmint API key or GCP credentials. Use environment variables or a secrets manager.